What is NAT?
Network Address Translation (NAT) allows a host that does not have a registered IP address to communicate with other hosts on the Internet. NAT has gained such wide-spread acceptance that the majority of enterprise networks today use private IP addresses for most hosts on their network and use a small block of public IP addresses, with NAT translating between the two.
Having come this far in your CCNA studies, you should be well aware of the IP header format. The IP packet header has several fields in it, the most well-known of which probably are the Source IP Address and Destination IP Address. NAT simply translates, or changes, one or both of these addresses inside a packet header as the packet passes through the router performing the NAT operation. This is what basic NAT operation is, nothing more, nothing less.
Purpose of NAT?
NAT is a feature that allows the internal network of an organization to appear to be using a different IP address space from the outside than what it is actually using. Thus, NAT allows an organization to use private IP addresses that are not globally routable and yet connect to the Internet by translating those private addresses into globally routable addresses. The beauty of NAT is that the hosts on the internal network using NAT to communicate to the outside world don’t have to be aware of the very existence of NAT. NAT configuration exists only on the router or another device typically at the boundary of the internal network. Due to this aspect of NAT, an organization can also change service providers without any changes to the IP addresses configured on individual hosts. Changing service providers also changes public IP addresses available to an enterprise. The device performing NAT can have its configuration modified and that’s all you need to do while changing your ISP.
Benefits of NAT
Internet Protocol (IP) or IPv4 as it is more precisely known uses addresses that are 32-bits long. As such the total address space of IP is from 0 to 232 – 1 = 4,294,967,295. In other words, over four billion unique IP addresses are available for assignment to hosts. These IP addresses are the registered IP addresses that are centrally administered. Though four billion may seem like a very large number, due to the explosive growth of the Internet over the years we have already depleted most of those IP addresses.
RFC 1918 specifies three blocks of IP address space reserved by Internet Assigned Numbers Authority (IANA) for private networks.
Table 10-1 Private IP Addresses
| Address Class | Number of Networks | Private Address Space |
| A | 1 | 10.0.0.0 – 10.255.255.255 |
| B | 16 | 172.16.0.0 – 172.31.255.255 |
| C | 256 | 192.168.0.0 – 192.168.255.255 |
An enterprise can assign these private IP addresses to internal host without the need for registered IP addresses. A router or other device can be used to perform Network Address Translation (NAT) to convert these private IP addresses to public IP addresses routable on the Internet.
Network Address Translation (NAT) is defined in RFC 1631. The original intention of NAT was to slow the depletion of available IP addresses by allowing many private IP addresses to be represented by some smaller number of public IP addresses. NAT was envisioned to be a temporary solution to the problem of IP version 4 address depletion. The permanent solution was a migration from IP version 4 to IP version 6 (IPv6). IPv6 has 128-bit addresses and a much larger address space expected to solve the issue of address scarcity forever. But NAT has been so successful that it has delayed the full IPv4 address exhaustion by several years.
NAT has also come to find other applications that do not directly relate to IP address conservation. One such NAT application is the merger of two companies and hence their internetworks. The two companies would previously have two separate internetworks. After the merger their two internetworks would have to be connected together. Unfortunately, when the two separate internetworks were first constructed several years ago, nobody had anticipated a future merger. So the designers of both internetworks chose to use the 10.0.0.0 address space. As a result, many IP addresses would be assigned to devices in both internetworks. NAT can be used as a temporary solution to connect the internetworks. Keep in mind that the best solution in such a situation is to re-address the new internetwork. But re-addressing can be a major project if all the devices have manually configured IP addresses. NAT can serve as an interim solution.
NAT allows organizations to solve the problem of IP address depletion when they want to connect new networks to the Internet. NAT allows organizations to connect their networks to the Internet without needing to have Network Information Center (NIC) registered IP addresses assigned to their internal systems.
There are organizations that already have registered IP addresses for hosts on an internal network but they want to hide those addresses from the Internet so that hackers cannot easily attack those hosts. If the host address is hidden, a degree of security is achieved. NAT can be useful in this situation where the motive is not primarily IP address preservation, but applying corporate security policies to your network traffic.
A major advantage of NAT is that it needs to be configured only on those few routers that would actually perform the NAT operation. The hosts or other routers not performing NAT operation don’t need any configuration changes.
Disadvantages of NAT
Network Address Translation (NAT) is all about changing IP addresses and port numbers inside an IP packet header which also creates some issues. Changing the content of an IP address or TCP port can change the meaning of some of the other fields, especially the checksum. For example, the checksum of an IP packet is calculated over the entire IP header. Therefore if the source or destination IP address (or both) change, the checksum has to be calculated again. The same is also true for the checksum in the TCP header. This number is calculated over the TCP header and data, and also over a pseudo-header that includes the source and destination IP addresses. Therefore, if an IP address or a port number changes, the TCP checksum must also change. NAT as implemented on Cisco routers performs these recalculations. This is extra work for the router performing NAT.
NAT should be transparent to the end systems that send packets through it. However, many applications use the IP addresses at the application layer. Information within the data field may be based on an IP address, or an IP address itself may be carried in the data field. If NAT translates an address in the IP header without being aware of the effects on the data, the application breaks.
As a matter of fact, Cisco’s NAT implementation goes beyond translating addresses in the IP header for the applications it supports. For the supported applications carrying IP address information in the application data, NAT makes the appropriate corrections to the data as well. This prevents the application from breaking due to NAT.
However, if the data fields are encrypted, NAT has no way of reading the data. Therefore, for NAT to function properly, neither the IP addresses nor any information derived from them (such as the TCP header checksum) can be encrypted. But this is not the case with virtual private networks (VPNs), for example, IPsec. With certain modes of IPsec, if an IP address is changed in an IPsec packet, the IPsec becomes meaningless and the VPN is broken. When any sort of encryption is used, you must perform NAT on the secure side before encryption, rather than in the encrypted path.
NAT is also viewed sometimes as part of a security plan, because it hides the details of the inside network from the outside world. A host with translated address may appear on the Internet with one address one day and with a different address on another day. But keep in mind that this is very weak security at best. It might slow down an attacker who wants to hit a particular host but it will not stop him if he is determined.
NAT Inside and Outside Addresses
Let’s define a few basic but important terms in the context of NAT. Before we jump into the definitions, have a look at Figure 10-1 in order to understand the context in which NAT typically operates.
Figure 10-1 NAT Context
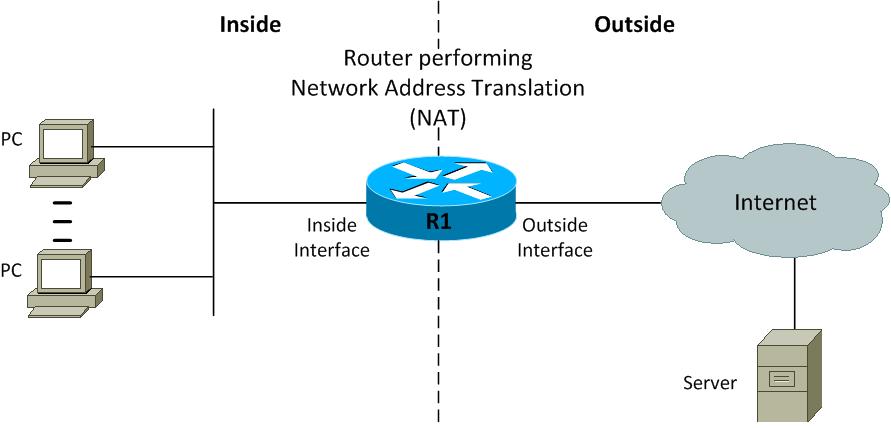
A device performing Network Address Translation (NAT) divides its universe into the inside and the outside. Typically the inside is a private enterprise with its internal network and hosts connected to that network. The outside on the other hand is the public Internet and the servers reachable over it. In addition to the notion of inside and outside, a Cisco NAT router classifies addresses as either local or global. A local address is an address that is seen by devices on the inside, and a global address is an address that is seen by devices on the outside.
Given these four terms, an address may be one of four types:
- 1. Inside local addresses are assigned to inside devices. These addresses are not advertised to the outside.
- 2. Inside global are addresses by which inside devices are known to the outside.
- 3. Outside local are addresses by which outside devices are known to the inside.
- 4. Outside global addresses are assigned to outside devices. These addresses are not advertised to the inside.
Types of NAT
In general, NAT is configured on a Cisco router that connects only two networks, and translates the inside local (private) addresses from the internal network into inside global (public) addresses. In most common scenarios the outside addresses are not translated so outside global and outside local addresses are the same. You can configure NAT in a way that it will advertise only a single address for your entire network to the outside world. Doing this effectively hides the addresses in your internal network from the hostile environment of the Internet. Thus, giving you some additional security and peace of mind as network administrator.
NAT has the following types:
- Static NAT: Static NAT performs static address translation allowing one-to-one mapping between local and global addresses. But you should keep in mind that static NAT requires you to have one registered public IP address for every host on your network. As such static NAT has no benefit in terms of IP address conservation. Nevertheless, static NAT is important for the sake of understanding NAT.
- Dynamic NAT: Dynamic NAT performs dynamic address translation mapping unregistered private IP addresses to registered public IP addresses from a pool of available registered IP addresses. You don’t have to statically configure your router to map an inside to an outside address as you would using static NAT. But yet you do have to have enough registered public IP addresses for everyone who’s going to communicate to the Internet. Even dynamic NAT does not help with the issue of IP address conservation.
- NAT Overload: NAT overload performs an overload mapping multiple unregistered private IP addresses to a single registered public IP address. It is a many-to-one mapping between private and public addresses and is accomplished using different port numbers. This method is also known as Port Address Translation (PAT). By using PAT or NAT overload, hundreds or even thousands of users can be connected to the Internet using only one real global IP address. This is the most popular NAT type which basically is a form of dynamic map but with multiple unregistered IP addresses mapped to a single registered IP address. Dynamic NAT is one-to-one while NAT Overload or PAT is many-to-one though both forms do the mapping dynamically. NAT Overload is the type of NAT that has enabled us not to run out of IP addresses on the Internet.

We will learn how to configure each of these three types of NAT in this chapter.
How NAT Operates?
Let’s have a look at Figure 10-2 that present a basic NAT scenario. We will explain the basics of NAT operation with the help of this scenario and the understanding you develop here should also help you understand the rest of the chapter.
Figure 10-2 Basic NAT Operation
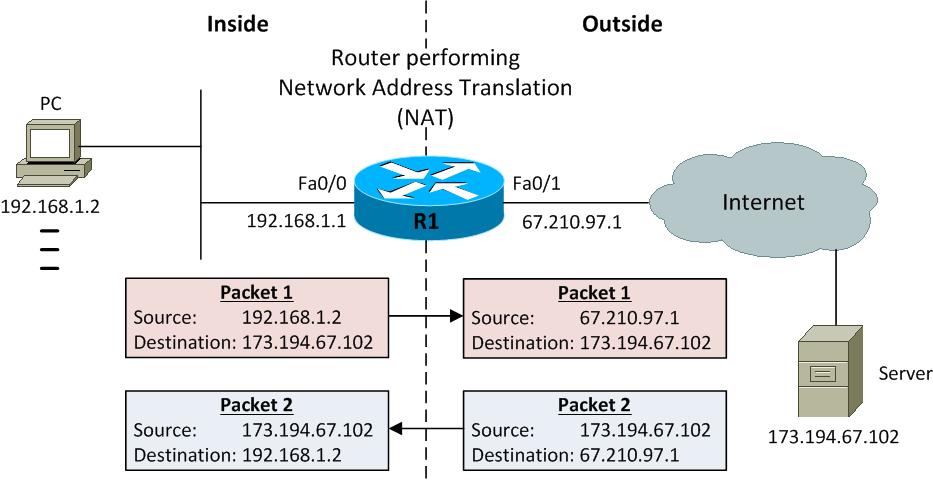
We have defined several terms related to NAT so far. It’s the right time to test that understanding in the context of Figure 10-2. R1 is the router performing NAT and has two interfaces: Fa0/0 as the inside interface while Fa0/1 is the outside interface. A PC having IP address 192.168.1.2 on the inside needs to communicate with a server having IP address 173.194.67.102 on the outside.
Table 10-2 NAT Address Types
| NAT Address Type | IP Address |
| Inside local | 192.168.1.2 |
| Inside global | 67.210.97.212 |
| Outside local | 173.194.67.102 |
| Outside global | 173.194.67.102 |
Let’s try to understand what happens to IP packets travelling back and forth between the PC and the server as they move across R1 – the router performing NAT operation. In plain simple words IP addresses in the header of those IP packets get re-written with R1 also keeping a record of these re-writes or translations in a table known not surprisingly as translation table.
Let’s first consider a packet that moves from inside to outside. This packet has source and destination IP addresses of 192.168.1.2 and 173.194.67.102 respectively. The packet enters router R1 at its inside interface Fa0/0 and exits the outside interface Fa0/1. Before the packet actually exits R1, the source address gets re-written. The inside local IP address 192.168.1.2 is replaced with the inside global IP address 67.210.97.212. The destination IP address is left untouched here so the outside local and outside global address are both 173.194.67.102. And some of you may have identified that the inside global address is in fact the IP address configured on the outside interface Fa0/1 of R1. To the outside world, the packet appears to have originated from the IP address 67.210.97.212 and the inside local IP address 192.168.1.2 is never known to the outside world! For packets moving in the opposite direction, from outside to inside, the destination IP address 67.210.97.212 gets re-written with 192.168.1.2 while the source IP address remains unchanged. The PC and server can communicate successfully yet the server or any entity on the outside does not know the real IP address of the PC.
In the coming sections we would learn in detail how to actually configure Network Address (NAT) on a Cisco router for all three types of NAT.
