Network security is only as strong as the weakest link, because a single weak point if exploited successfully would be enough for an intruder. That weak link can be the data link layer or layer 2 of the OSI reference model. We can secure the posterior of our network protecting it from external threats but it is equally important to secure the interior of the network as several threats actually originate from the inside. Like routers, Cisco switches too have their own set of network security requirements. As a matter of fact switches may turn out to be that weak area if not properly secured. Access to switches can be a convenient entry point for attackers who want to gain access to a corporate network. With access to a switch, an attacker can launch all types of attacks from within the network. The security mechanisms that are meant to protect network perimeter would not be enough to stop these attacks simply because they originate from inside the network. For example attackers can spoof the MAC and IP addresses of critical servers to do a great deal of damage. The can even set up rogue wireless access points to provide continued access.
Port Security
You can use the port security feature on Cisco switches to restrict who can access the network by connecting to a switch port. This feature is used to limit and identify the MAC addresses of the systems that are allowed to access the port. You can configure a switch port to be secure and can also specify which MAC addresses are allowed to access the port. The secure switch port does not forward frames with source MAC addresses outside the group of defined MAC addresses for that port.
Port security allows you to manually specify MAC addresses for a port or permit the switch to dynamically learn a limited number of MAC addresses from incoming frames. By limiting the number of permitted MAC addresses on a port to just one, you can you can make sure that just one system can connect to the port, preventing any unauthorized exapansion of the network by attaching a hub or switch.
When a secure port receives a frame, the source MAC address of the frame is compared to the list of secure MAC addresses associated with the port. These secure MAC addresses are either manually configured or auto-configured or learned on the port. If the source MAC address of a frame differs from the list of secure addresses, the port either shuts down or the port drops incoming frames from unauthorized host. The default behavior of a secure port is to shut down until it is administratively enabled. The behavior of the port depends on how you configure it to respond to a security violation.
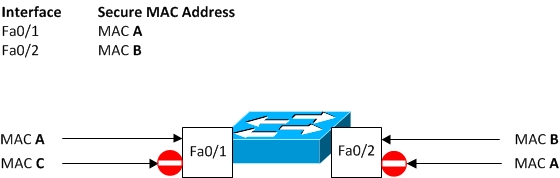
In Figure 8-3, switch port Fa0/1 will only allow those incoming frames that have source MAC address of MAC A. This port will block traffic with source MAC address of MAC C or any other frame having a source MAC address other than MAC A. Similarly, port Fa0/2 will allow traffic with source MAC address of MAC B only. This port will block all other source MAC addresses including MAC A. Despite the fact that MAC A is allowed on port Fa0/1, it is blocked on port Fa0/2 because secure (allowed) MAC addresses are specific to individual switch ports.
Figure 8-3 Port Security
I would strongly recommend configuring the port security feature to shut down a port instead of just dropping packets from hosts with unauthorized addresses. If port security does not shut down a port, it is still possible that the port will be disabled due to too much traffic load from an attack.
Port security is a useful feature as it protects against too many MAC addresses per ports and can dictate which MAC address is allowed to connecte against which port. However, if the hacker knows which MAC address is permitted on that port, he will gain access to the network by spoofing the MAC address. Port security also prevents unauthorized extension of the LAN in case a user decides to attach a hub to connect additional hosts. You have to allow only a single MAC address on the secure port to prevent this sort of extension. Also, if you are concerned about spoofed MAC addresses to bypass port security, then consider implementing IEEE 802.1X authentication mechanism.
Let’s see how we can configure a switch port with one specific secure MAC address. If any other device plugs into this interface not using that specific MAC address, the port will go into an err-disabled state that must be cleared by an administrator.
Switch(config)#interface Fa0/0
Switch(config-if)#switchport mode access
Switch(config-if)#switchport port-security
Switch(config-if)#switchport port-security mac-address 1234.5678.9ABC
VLAN Hopping
VLANs simplfy network maintenance, improve performance, and provide security by isolating traffic from different VLANs. You may recall, that inter-VLAN communication is not possible without going through a router. But, a technique known as VLAN hopping allows traffic from one VLAN to be seen by another VLAN without first crossing a router. In some situations, attackers can even sniff data and obtain passwords and other sensitive information. The attack works by taking wrongful advantage of an incorrectly configured trunk port. As you learnt, trunk ports pass traffic from all VLANs (1 – 4094) across the same physical link, generally between switches. The data frames moving across these trunk links are encapsulated with IEEE 802.1Q or ISL to identify which VLAN a frame belongs to.
We will discuss a basic VLAN hopping attack that uses a rogue trunk link, as shown in Figure 8-4. In this attack, the attcker takes advantage of the default automatic trunking configuration found on most switches. The attacker first gets access to a vacant port on a switch and then configures a system, most likely a laptop computer, present itself as a switch. It is possible to do so if the system is fitted with an 802.1Q or ISL capable NIC, using appropriate software that usually comes with the NIC itself.
Figure 8-4 VLAN Hopping Attack
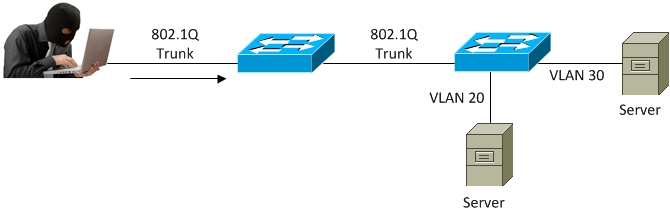
The attacker communicates with the switch with Dynamic Trunking Protocol (DTP) messages, trying to trick the switch into thinking it is another switch that needs to trunk. If a trunk is successfully established between the attacker’s system and the switch, the attacker can gain access to all the VLANs allowed on the trunk port. In order to succeed, this attack requires a switch port that supports trunking such as desirable or auto. The end result is that the attacker is a member of all the VLANs that are trunked on the switch and can hop on all those VLANs, sending and receiving traffic.
This sort of simple but effective VLAN hopping attack can be launched in one of two ways:
- Generating DTP messages from the attacking host to cause the switch to establish a trunk with the host. Once a trunk is established, the attacker can send and receive traffic tagged with the target VLAN to reach any other host like a server in that VLAN, because the switch then delivers packets to the destination.
- Introducing an actual rogue switch and turning trunking on can also establish a trunk with the victim switch. The attacker can then access all the VLANs on the target switch from the rogue switch.
The best way to prevent a basic VLAN hopping attack is to turn off trunking all switch ports except the ones that specifically require trunking. All user ports should be configured with the following commands:
- switchport mode access: This command permanently sets the switch port to a non-trunking mode and is just good enough for all switch ports supposed to be connected to user PCs.
- switchport nonegotiate This command can additionally be used to disable generation of DTP messages. Though, a port configured with switchport mode access can never become a trunk, yet disabling DTP reduces unwanted DTP frames on the link.
On switch ports that do require trunking, DTP should be disabled using command switchport nonegotiate and trunking should be manually configured using command switchport mode trunk in interface configuration mode.
